Earlier than you submit questions or dangerous opinions, see the FAQ
https://sisik.eu/bugjaeger_faq
Bugjaeger tries to provide the professional instruments utilized by Android builders for higher management and deep understanding of your Android system internals.
Multitool that may prevent the effort of carrying a laptop computer.
For those who’re an Android energy person, developer, geek, or hacker, this app needs to be in your toolkit.
The way to use
1.) Allow developer choices and USB debugging in your goal system (https://developer.android.com/studio/debug/dev-options)
Word: On Huawei units you would possibly first have to activate USB tethering earlier than you allow USB debugging
2.) Join the system the place you’ve got put in this app to the goal system through USB OTG cable
3.) Enable the app to entry USB system and ensure goal system authorizes USB debugging
Inspecting system internals, working shell scripts, checking logs, making screenshots, sideloading, and plenty of extra duties which are usually performed in your laptop computer can now be carried out immediately between 2 cellular units.
This app works as type of Android to Android ADB (Android Debug Bridge) – it presents some options just like ADB (Android Debug Bridge), however as a substitute of working in your growth machine, it runs immediately in your Android system.
You join your goal system by USB OTG cable or by WiFi and you can mess around with the system.
ADB protocol is supported additionally by Android units apart from telephones & tablets. That signifies that you must also be capable to management your Android TV, Put on OS watch, and even Raspberry Pi with Android Issues OS and Oculus VR.
Principal options
– working shell scripts on course system
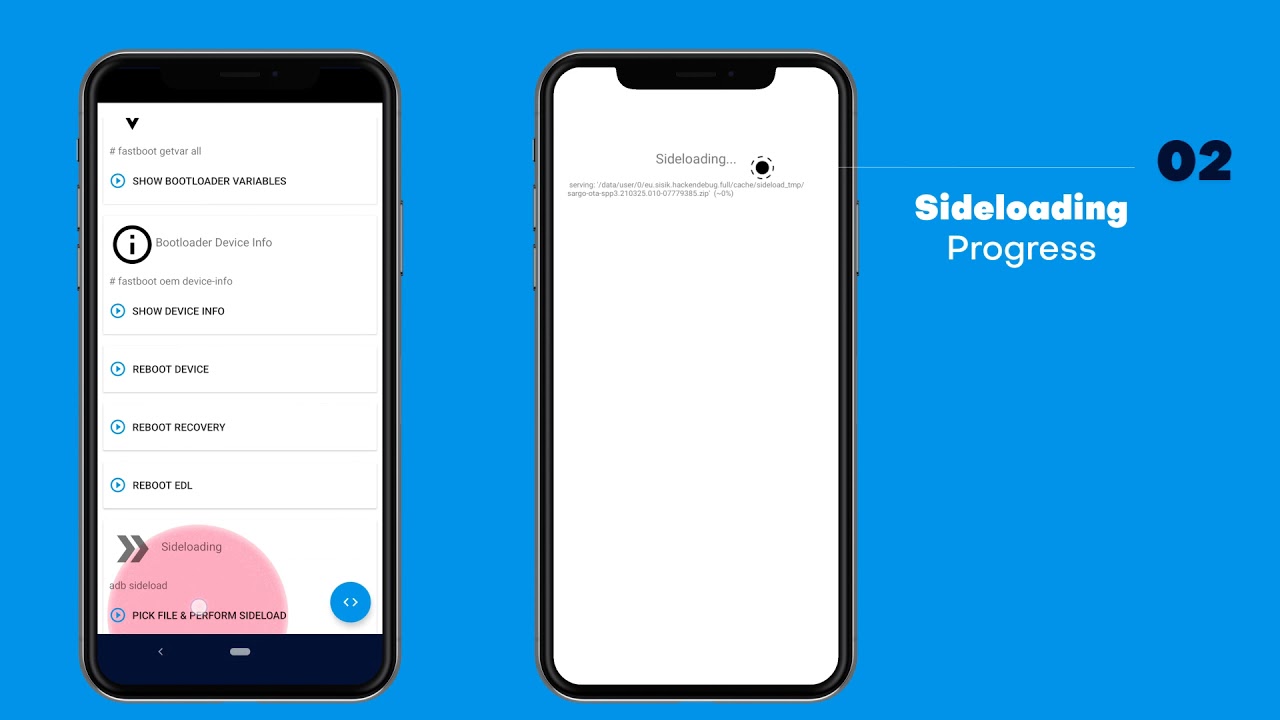
– sideload common/cut up APKs (e.g. to Oculus Quest VR)
– sideload/flash AOSP photographs (e.g. Android Preview on Pixel)
– distant interactive shell
– mirroring display
– studying, filtering, and exporting system logs (logcat)
– pull APK recordsdata
– ADB backups, inspecting and extracting content material of backup recordsdata
– screenshots
– performing varied ADB instructions for controlling your system (rebooting, going to bootloader, rotating display, killing working apps, …)
– uninstalling and putting in packages, checking varied particulars about put in apps
– copying apps between telephones
– monitoring the processes, displaying extra data associated to processes, killing processes
– displaying varied particulars about Android model(e.g., SDK model, Android ID,..), Linux kernel, cpu, abi, show
– displaying battery particulars (like e.g., temperature, well being, know-how, voltage,..)
– file administration – pushing and pulling recordsdata from system, shopping the file system
– search and hook up with Android units in your community that configured adbd to pay attention on port 5555
– studying bootloader variables & information through fastboot protocol (e.g. dump some hw information, safety state, or if the system was tampered)
– exec fastboot instructions
For some methods and examples of what you are able to do, see
https://www.sisik.eu/weblog/tag:bugjaeger
For beginning a youtube video or url in browser, add following customized command (or paste this into shell) within the first tab
am begin -a android.intent.motion.VIEW -d “yt_url”
For those who favored this app, take a look at the ad-free premium model which additionally comprises extra options
https://play.google.com/retailer/apps/particulars?id=eu.sisik.hackendebug.full
Necessities
– Enabled USB debugging in Developer choices and authorise the event system
– Fastboot protocol help
Please notice
This app makes use of the conventional method of speaking with Android units which requires authorisation.
The app doesn’t bypass Android’s safety mechanisms or something comparable!
This implies you will not be capable to do some privileged duties on non-rooted units.


